RE: GP4 & Multiple Monitors on Win 7
Posted by Lumpy20
| Registered: 13 years ago |
To add to my previous post I have ran GPXPatch and the first past of the error log file (124 pages long) might help.
Regards, KH
Starting log
GPxPatch version: 3.93
GPx version detected: decrypted GP4 v1.02
Verbosity level is 0
OS version info: Windows XP Service Pack 2 build 2600
Total physical memory: 1023 MB (free: 1023 MB)
Debugging gp4.exe
Waiting for debug events...
Injecting DLL loading code...
Injection succesful
First chance exception
Exception address: 0x778ebce7
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x00c42151
First chance exception
Exception address: 0x778ebce7
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x00c44c05
First chance exception
Exception address: 0x0054cf4f
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to write to virtual address 0x00b4a000
First chance exception
Exception address: 0x77dc2d86
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
First chance exception
Exception address: 0x77dc2d86
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
First chance exception
Exception address: 0x77dc2d86
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
First chance exception
Exception address: 0x77dc2d86
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
-------
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
Unhandled exception
Exception address: 0x00509fbd
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x58070083
Stack trace:
00509FBD: Program Files\Infogrames\Grand Prix 4\GPxPatch.exe! <no symbol>
72CEA535: Windows\system32\WINMM.dll! timeEndPeriod + 1354 bytes
72CEA434: Windows\system32\WINMM.dll! timeEndPeriod + 1097 bytes
778FED6C: Windows\system32\kernel32.dll! BaseThreadInitThunk + 18 bytes
77DD377B: Windows\SYSTEM32\ntdll.dll! RtlInitializeExceptionChain + 239 bytes
77DD374E: Windows\SYSTEM32\ntdll.dll! RtlInitializeExceptionChain + 194 bytes
Registers:
EAX=58070083 ECX=58070083 ESI=00000010
EBX=00000000 EDX=77DB7094 EDI=0050A190
CS:EIP=001B:00509FBD
SS:ESP=0023:0266FE6C EBP=0266FEB8
DS=0023 ES=0023 FS=003B GS=0000
Flags=00010202
Stack dump:
0266fe6c: 0054e75d 0050a190 00000010 0266feb8 '].T...P.......f.'
--------
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
Stack trace:
77DC2D86: Windows\SYSTEM32\ntdll.dll! RtlAllocateHeap + 32 bytes
643793DE: Windows\AppPatch\AcXtrnal.DLL! <no symbol>
005DEBCC: Program Files\Infogrames\Grand Prix 4\GPxPatch.exe! <no symbol>
005DFF18: Program Files\Infogrames\Grand Prix 4\GPxPatch.exe! <no symbol>
005DDFC0: Program Files\Infogrames\Grand Prix 4\GPxPatch.exe! <no symbol>
778FED6C: Windows\system32\kernel32.dll! BaseThreadInitThunk + 18 bytes
77DD377B: Windows\SYSTEM32\ntdll.dll! RtlInitializeExceptionChain + 239 bytes
77DD374E: Windows\SYSTEM32\ntdll.dll! RtlInitializeExceptionChain + 194 bytes
Registers:
EAX=01040A60 ECX=7FFDF000 ESI=00000000
EBX=58070083 EDX=00000057 EDI=000000A0
CS:EIP=001B:77DC2D86
SS:ESP=0023:000311EC EBP=00031258
DS=0023 ES=0023 FS=003B GS=0000
Flags=00210293
Stack dump:
000311ec: 000000a0 00000008 00000080 00000000 '................'
Regards, KH
Starting log
GPxPatch version: 3.93
GPx version detected: decrypted GP4 v1.02
Verbosity level is 0
OS version info: Windows XP Service Pack 2 build 2600
Total physical memory: 1023 MB (free: 1023 MB)
Debugging gp4.exe
Waiting for debug events...
Injecting DLL loading code...
Injection succesful
First chance exception
Exception address: 0x778ebce7
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x00c42151
First chance exception
Exception address: 0x778ebce7
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x00c44c05
First chance exception
Exception address: 0x0054cf4f
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to write to virtual address 0x00b4a000
First chance exception
Exception address: 0x77dc2d86
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
First chance exception
Exception address: 0x77dc2d86
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
First chance exception
Exception address: 0x77dc2d86
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
First chance exception
Exception address: 0x77dc2d86
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
-------
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
Unhandled exception
Exception address: 0x00509fbd
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x58070083
Stack trace:
00509FBD: Program Files\Infogrames\Grand Prix 4\GPxPatch.exe! <no symbol>
72CEA535: Windows\system32\WINMM.dll! timeEndPeriod + 1354 bytes
72CEA434: Windows\system32\WINMM.dll! timeEndPeriod + 1097 bytes
778FED6C: Windows\system32\kernel32.dll! BaseThreadInitThunk + 18 bytes
77DD377B: Windows\SYSTEM32\ntdll.dll! RtlInitializeExceptionChain + 239 bytes
77DD374E: Windows\SYSTEM32\ntdll.dll! RtlInitializeExceptionChain + 194 bytes
Registers:
EAX=58070083 ECX=58070083 ESI=00000010
EBX=00000000 EDX=77DB7094 EDI=0050A190
CS:EIP=001B:00509FBD
SS:ESP=0023:0266FE6C EBP=0266FEB8
DS=0023 ES=0023 FS=003B GS=0000
Flags=00010202
Stack dump:
0266fe6c: 0054e75d 0050a190 00000010 0266feb8 '].T...P.......f.'
--------
Exception code: EXCEPTION_ACCESS_VIOLATION
Process tried to read from virtual address 0x580700c7
Stack trace:
77DC2D86: Windows\SYSTEM32\ntdll.dll! RtlAllocateHeap + 32 bytes
643793DE: Windows\AppPatch\AcXtrnal.DLL! <no symbol>
005DEBCC: Program Files\Infogrames\Grand Prix 4\GPxPatch.exe! <no symbol>
005DFF18: Program Files\Infogrames\Grand Prix 4\GPxPatch.exe! <no symbol>
005DDFC0: Program Files\Infogrames\Grand Prix 4\GPxPatch.exe! <no symbol>
778FED6C: Windows\system32\kernel32.dll! BaseThreadInitThunk + 18 bytes
77DD377B: Windows\SYSTEM32\ntdll.dll! RtlInitializeExceptionChain + 239 bytes
77DD374E: Windows\SYSTEM32\ntdll.dll! RtlInitializeExceptionChain + 194 bytes
Registers:
EAX=01040A60 ECX=7FFDF000 ESI=00000000
EBX=58070083 EDX=00000057 EDI=000000A0
CS:EIP=001B:77DC2D86
SS:ESP=0023:000311EC EBP=00031258
DS=0023 ES=0023 FS=003B GS=0000
Flags=00210293
Stack dump:
000311ec: 000000a0 00000008 00000080 00000000 '................'
| Registered: 20 years ago |
| Registered: 13 years ago |
Hi,
I have the complete log but it is 124 pages long in Word pad.
Do you want me to list the entire log?
Also installed GP3, updated to GP3-2000, on the same PC and get some crashes on exit although I can play a full game.
GP3-2000 (and GP3) crashes when I try to calibrate the graphics card. If I skip this and just run GP3 and set graphics manually all is fwine except on exit as mentioned.
Another note I am using Microsoft Security Essentials for Firewall and AV if this makes a difference.
Regards, KH
I have the complete log but it is 124 pages long in Word pad.
Do you want me to list the entire log?
Also installed GP3, updated to GP3-2000, on the same PC and get some crashes on exit although I can play a full game.
GP3-2000 (and GP3) crashes when I try to calibrate the graphics card. If I skip this and just run GP3 and set graphics manually all is fwine except on exit as mentioned.
Another note I am using Microsoft Security Essentials for Firewall and AV if this makes a difference.
Regards, KH
| Registered: 12 years ago |
Lumpy20 écrivait:
-------------------------------------------------------
> Hi,
> I have the complete log but it is 124 pages long in Word pad.
>
> Do you want me to list the entire log?
>
I think pasting one of the stack dump logs mentioned by Laurent will be enough.
> Also installed GP3, updated to GP3-2000, on the
> same PC and get some crashes on exit although I
> can play a full game.
>
Do you have GPxPatch in debug mode ? If so, that sounds normal to me. (just uncheck the Debug mode case)
> GP3-2000 (and GP3) crashes when I try to
> calibrate the graphics card. If I skip this and
> just run GP3 and set graphics manually all is
> fwine except on exit as mentioned.
>
That's an usual issue. GP3 isn't comfortable with multi-screens. You DON'T have to calibrate the graphics as asked by the game, except the very first time you run it after it's first install. (after that, NEVER calibrate the graphics again)


-------------------------------------------------------
> Hi,
> I have the complete log but it is 124 pages long in Word pad.
>
> Do you want me to list the entire log?
>
I think pasting one of the stack dump logs mentioned by Laurent will be enough.
> Also installed GP3, updated to GP3-2000, on the
> same PC and get some crashes on exit although I
> can play a full game.
>
Do you have GPxPatch in debug mode ? If so, that sounds normal to me. (just uncheck the Debug mode case)
> GP3-2000 (and GP3) crashes when I try to
> calibrate the graphics card. If I skip this and
> just run GP3 and set graphics manually all is
> fwine except on exit as mentioned.
>
That's an usual issue. GP3 isn't comfortable with multi-screens. You DON'T have to calibrate the graphics as asked by the game, except the very first time you run it after it's first install. (after that, NEVER calibrate the graphics again)


| Registered: 18 years ago |
EricMoinet schrieb:
-------------------------------------------------------
> Lumpy20 écrivait:
> --------------------------------------------------
> > GP3-2000 (and GP3) crashes when I try to
> > calibrate the graphics card. If I skip this and
> > just run GP3 and set graphics manually all is
> > fwine except on exit as mentioned.
> >
>
> That's an usual issue. GP3 isn't comfortable with
> multi-screens. You DON'T have to calibrate the
> graphics as asked by the game, except the very
> first time you run it after it's first install.
> (after that, NEVER calibrate the graphics again)
the crash when calibrating the graphics is usually related to gpxpatch and/or a decrypted exe. make sure you run gp3/4 at least once immeadiately after installation, without applying any patches or other stuff
used to be GPGSL's Nick Heidfeld
-------------------------------------------------------
> Lumpy20 écrivait:
> --------------------------------------------------
> > GP3-2000 (and GP3) crashes when I try to
> > calibrate the graphics card. If I skip this and
> > just run GP3 and set graphics manually all is
> > fwine except on exit as mentioned.
> >
>
> That's an usual issue. GP3 isn't comfortable with
> multi-screens. You DON'T have to calibrate the
> graphics as asked by the game, except the very
> first time you run it after it's first install.
> (after that, NEVER calibrate the graphics again)
the crash when calibrating the graphics is usually related to gpxpatch and/or a decrypted exe. make sure you run gp3/4 at least once immeadiately after installation, without applying any patches or other stuff
used to be GPGSL's Nick Heidfeld
| Registered: 18 years ago |
sorry to ask, but the video controller supports more than one monitor, right?
----signature--------------------------------------------------------
RELEASE => Physics (under FIA Technical Regulations)
MagicDatas? Setups? Pit Stop Strategies? Track Specific Performances? Up2Date GP?
Power Torque Curve? Where's this stuff? All download is available at ..
----signature--------------------------------------------------------
RELEASE => Physics (under FIA Technical Regulations)
MagicDatas? Setups? Pit Stop Strategies? Track Specific Performances? Up2Date GP?
Power Torque Curve? Where's this stuff? All download is available at ..
| Registered: 14 years ago |
yes but its not possible to let the 2 screens work as 1 whole screen. you see 2x gp4 in both monitors
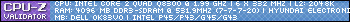
PC: 
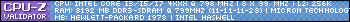
Laptop:
Twitter: MisterShine13
Laptop:
Twitter: MisterShine13
| Registered: 19 years ago |
| Registered: 10 years ago |
| Registered: 19 years ago |
Sorry, only registered users may post in this forum.
GP3 CarshapesGP3 CART & other CarsGP3 CART & other TracksGP3 CockpitsGP3 Editors / UtilitiesGP3 F1 CarsGP3 F1 TracksGP3 Fictional CarsGP3 Fictional TracksGP3 Graphics (Software Mode)GP3 HelmetsGP3 MiscGP3 Misc. GraphicsGP3 PatchesGP3 PitcrewsGP3 Season PackagesGP3 SetupsGP3 SoundsGP3 TeamartGP3 Trackgraphics
Maintainer: mortal, stephan | Design: stephan, Lo2k | Moderatoren: mortal, TomMK, Noog, stephan | Downloads: Lo2k | Supported by: Atlassian Experts Berlin | Forum Rules | Policy



